Looking for design inspiration? Browse our curated collections!
10 Years Ago

A major bug called "Heartbleed' was recently discovered that could have left millions of user passwords / credit card numbers vulnerable to exploitation by hackers. It affects as much as 66% of the servers in the world.
Here are a few links to more info on this:
http://www.washingtonpost.com/news/morning-mix/wp/2014/04/09/major-bug-called-heartbleed-exposes-data-across-the-internet/
http://news.netcraft.com/archives/2014/04/08/half-a-million-widely-trusted-websites-vulnerable-to-heartbleed-bug.html
https://gigaom.com/2014/04/08/heres-everything-you-need-to-know-about-the-heartbleed-web-security-flaw/
This is serious.
I would suggest everyone change their passwords now; not just on FAA but e-mail, social media, etc.
Reply Order
10 Years Ago
Thank you, Lance. edit................I wish you'd add a "Important" to your thread title...........please.....more explanatory for us.
10 Years Ago
I tried your link............as follows:
Secure Connection Failed
An error occurred during a connection to gigaom.com. Peer's Certificate has been revoked. (Error code: sec_error_revoked_certificate)
The page you are trying to view cannot be shown because the authenticity of the received data could not be verified.
Please contact the website owners to inform them of this problem. Alternatively, use the command found in the help menu to report this broken site.
10 Years Ago
Hmm.. Don't know what's going on there. Worked fine for me. Just Google "Heartbleed" and read as much as you can about it.
10 Years Ago
from the comments page...............FAA - please note......................
Patching is not the only thing you have to do. You also need to revoke and re-certify ALL of your certificates because the flaw allowed the hackers to steal your secret key and they can use it to spoof your site even AFTER being patched.
10 Years Ago
Lance,
Thanks, I think! What to do? Probably any info is already gone,since this was found about 12 hours ago or more. Where to start?
Rich
10 Years Ago
@Rich
We can only do what we can do. Changing your password is a good start, though. O_o
10 Years Ago
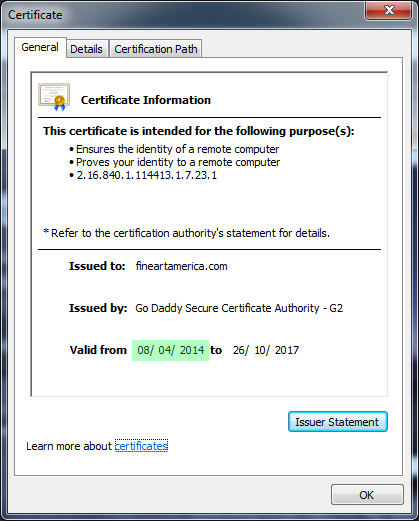
FAA re-issued their certificate yesterday, so it's safe to change your password on here:
10 Years Ago
For what it's worth, this shows some of the site affected/unaffected http://mashable.com/2014/04/09/heartbleed-bug-websites-affected/?utm_cid=mash-com-fb-main-link
10 Years Ago
UPDATE:
Here are some test sites:
http://www.theatlantic.com/technology/archive/2014/04/how-to-check-if-a-site-is-safe-from-heartbleed/360417/
10 Years Ago
Changing your password won't help if the site hasn't updated. FAA did update theirs, so changing the FAA password will help, but if you change it on a site that hasn't updated yet, it will not matter.
10 Years Ago
Exactly, Roseann...the hackers will just pick up your new password.
SO use the test sites offered in my last link to individually check each url that you use...a laborious job,but very important...PARTIULARLY for banking!!
10 Years Ago
Here's a place where you can enter a URL and test it for the Heartbleed vulnerability.
http://filippo.io/Heartbleed/
BTW, one of the best sources for the latest security info is http://krebsonsecurity.com/.
10 Years Ago
I just typed-in paypal.com at the test site, and got a warning stating to take immediate action. Does that mean we should all change our passwords, etc to paypal?
10 Years Ago
https://www.ssllabs.com/ssltest/analyze.html?d=paypal.com
two passes and one fail for paypal....
10 Years Ago
Marlene,
Looking at the test times, it got a Pass, Fail, Pass, in that order. Under that it states this: "Warning: Inconsistent server configuration".
10 Years Ago
There's an add on for chrome called chromebleed, I can't say how accurate it is but it flagged one page here, Paypal is ok. I found one other website it flagged yesterday - Canadian Geographic photo club, but it's ok today. Supposedly the banks are ok. Flickr was supposed to be compromised as was Yahoo but chromebleed isn't flagging them.
10 Years Ago
This is a hard core url checking site...use it for your BANKING and anything with your banking info!!
10 Years Ago
SSLLAbs is checking the SSL portion of a site, whether it is working and configured properly. It is not checking specifically for Heartbleed. In other words if your bank checks out, don't count on the site to be free of Heartbleed.
The "inconsistent" message is referring to the 23.73.82.234 which is not Paypal but an advertisement associated with Akamai Technologies Inc. This would not be SSL to begin with because you aren't logging into the ad. We see a ton of Akamai Technologies traffic on our network because they are responsible for a lot of the ad banners you see on websites you visit.
http://filippo.io/Heartbleed/ shows Paypal as being clean.
10 Years Ago
When you cannot trust the security of the software that provides cryptographic security for the internet, you're in deep do-do.
Luckily, my bank and hosting company (Suntrust, hostgator) were on the non-vulnerable list.
But a warning:
I do personal email thru my own self-hosted domain on hostgator. Last night when I did my email, I got invalid certificate warnings. Yet, hostgator is on this list of so-called safe sites:
https://github.com/musalbas/heartbleed-masstest/blob/master/top10000.txt
Which tells me that the test evaluating them as being safe was done after they updated their certificates and that before that, they were vulnerable!
The bottom line?
Any site that is on a list OR tests thru a testing website as "safe" might be now, but may previously not have been. So, because they may have been vulnerable, I would change the password. Test each site to see if it is now safe, then change.
10 Years Ago
Although it was said already in this thread, I wanted to reiterate that FAA is okay. As soon as Sean was aware, a few days ago, he acted.
10 Years Ago
If any of you use LastPass, the free password storage and creator, there is in the vault a security check. By running that check you will get a list of sites you use that have been affected.
I don't know if any of you use a password generator but I have used LastPass for 2 years and love it. Now I sound like a commercial..sorry. But if you have it you can use it to check for Heartbleed
10 Years Ago
It get's "worser'!!!
The Heartbleed vulnerability went undetected for about two years and can be exploited without leaving a trace, so experts and consumers fear attackers may have compromised large numbers of networks without their knowledge.
"Worsest!"
"I am waiting for a patch," said Jeff Moss, a security adviser to the U.S. Department of Homeland Security and founder of the Def Con hacking conference. Def Con's network uses an enterprise firewall from McAfee, which is owned by Intel Corp's security division.
Rich
10 Years Ago
Marlene,
Don't know nuttin' about no emails............
But if this has been squirming around for almost 2 full years, we be screwed!
Rich
10 Years Ago
I noticed yesterday that there was a little 'x' on my Norton 360 Icon in my system tray. I tried to do all my scans but it wouldn't do a full system scan...it stopped in the middle of it and kept saying that I need to "FIX" this now. Well after 3 tries I decided to check my add ons and for some weird reason some of the functions of my Norton software had been disabled. I did NOT disable them! So I enabled them and could do a full system scan. Now my Norton icon has a green check mark in place of that red 'x'. So I think all is well. Another thing I noticed right before I saw the red 'x' on the icon, was that my mouse was skipping around in Photoshop (as if commandeered remotely by someone)...this really freaked me out! After the full scan, the mouse was behaving normally.
Our local news said not to change passwords willy nilly because of the reasons above but also actually going to the sites and changing your passwords leaves you open to vulnerability in the process of changing them. So I haven't changed any yet.
Here is some good info from Symantec:
http://www.symantec.com/outbreak/?id=heartbleed
10 Years Ago
Joy, same thing suddenly with Kaspersky. Thought it odd, thought nothing much of it.....then!
Had to re-enable too.
Anyone else?


